Intrusion Prevention3: Difference between revisions
No edit summary |
No edit summary |
||
| Line 31: | Line 31: | ||
== About Intrusion Prevention == | == About Intrusion Prevention == | ||
Intrusion Prevention is an [http://en.wikipedia.org/wiki/Intrusion_detection_systems Intrusion Detection system] that detects malicious activity on your network. To detect malicious activity, Intrusion Prevention uses signature detection, a method that draws upon a database of known attack patterns. If Intrusion Prevention detects malicious activity, the [http://en.wikipedia.org/wiki/Session_%28computer_science%29 session] for that activity | Intrusion Prevention is an [http://en.wikipedia.org/wiki/Intrusion_detection_systems Intrusion Detection system] that detects malicious activity on your network. | ||
To detect malicious activity, Intrusion Prevention uses signature detection, a method that draws upon a database of known attack patterns. | |||
If Intrusion Prevention detects malicious activity, the [http://en.wikipedia.org/wiki/Session_%28computer_science%29 session] for that activity can be logged or blocked. | |||
''Note:'' Intrusion Prevention installs but is off by default. | ''Note:'' Intrusion Prevention installs but is off by default. | ||
| Line 37: | Line 39: | ||
''Note:'' Intrusion Prevention requires at least 2 gigabytes of RAM. | ''Note:'' Intrusion Prevention requires at least 2 gigabytes of RAM. | ||
=== Signatures & Actions === | |||
A signature matches behavior patterns such as plain text in a connection or the number of times a particular host attempts to open TCP connections to another host. | |||
When the conditions for a signature are met, the incident is either logged to the event log without distruption to the session or blocked which both logs the incident but breaks the connection causing that session to "stop". | |||
The default signature database is automatically populated and updated on a regular basis, usually every 2-3 days. | |||
You can add custom signatures if you wish but it is not neccessary. | |||
While it is tempting to block all signatures, there is a high potential for false positives which could cause legitmate traffic to stop working. | |||
It is therefore recommmnted that signatures are logged, the event log reviewed, and if the incident is deemed problematic, change the signature action to block. | |||
It may be similarly temping to log all signatures. | |||
While logging won't stop traffic it will consume system processing resources (CPU and memory) and potentially fill your event log with false positives. | |||
A signature can also be disabled. This means is it not loaded into the engine at all. | |||
Signature actions are set by rules. In the context of signatures, actions are recommmended only. | |||
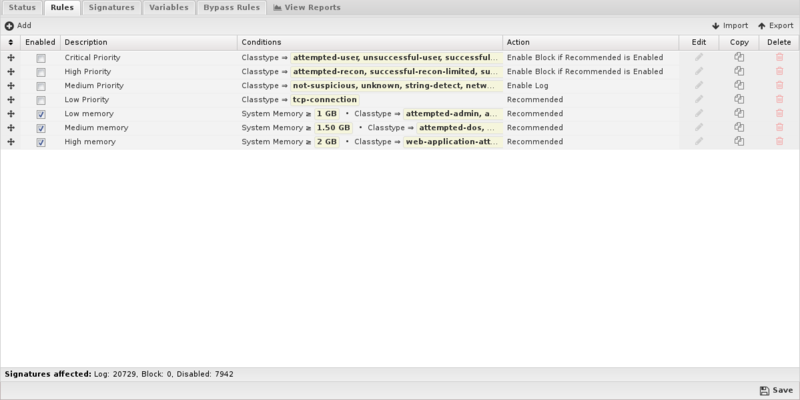
=== Rules === | |||
Rules match characteristics of signatures and if matched, set signature action as follows: | |||
* Recommended | |||
* Enable Log | |||
* Enable Block if Recommended is Log | |||
* Emable Block | |||
* Disable | |||
Conditions: | |||
* Signature Identifier | |||
* Group Identifier | |||
* Category | |||
* Classtype | |||
* Message | |||
* Protocol | |||
* Source Address | |||
* Source Port | |||
* Destination Address | |||
* Destination Port | |||
* Any part of signature | |||
* Custom signature | |||
* Recommended Action | |||
* System Memory | |||
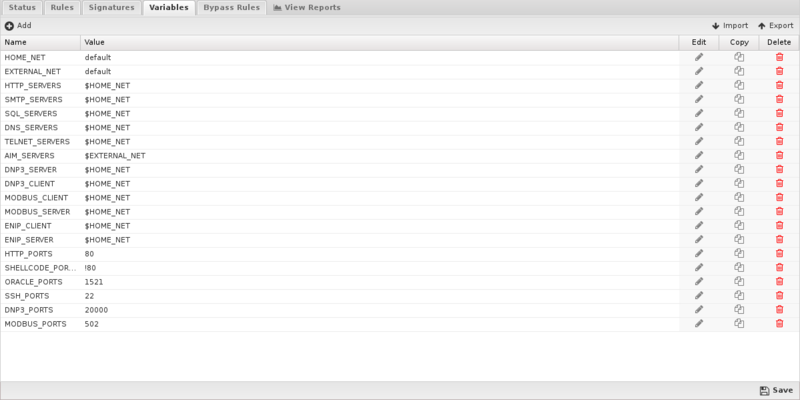
=== Variables === | |||
Variables define common attributes like the home network and ports. Under most circumstances these should be left alone. | |||
For HOME_NET and EXTERNAL_NET, the default values ensures these are automatically calculated. | |||
=== Memory === | |||
Intrusion Prevention can be memory intensive. How much is used is a combination of the number of signatures enabled for Log or Block and the amount of traffic that goes through your system. | |||
== Settings == | == Settings == | ||
| Line 42: | Line 97: | ||
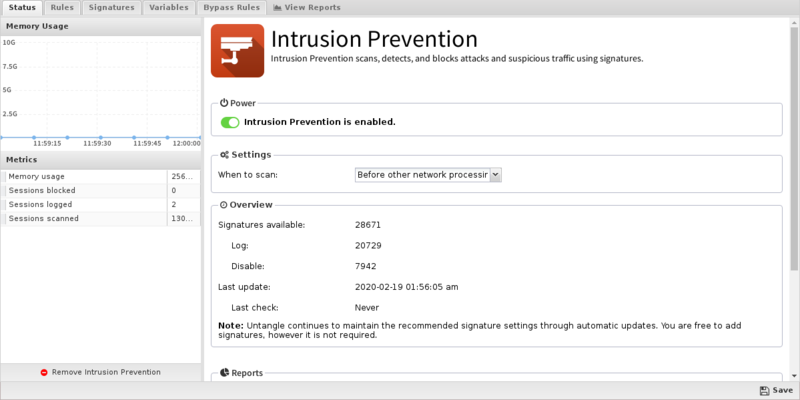
=== Status === | === Status === | ||
The Status tab | The Status tab shows the following information: | ||
* Memory Usage. The amount of system memory the IPS engine is using compared to your installed system memory. | |||
* Metrics. The number of blocked, logged, and scanned sessions. | |||
* Overview. Signatures and Signature Updates. | |||
** Signatures. Total number of signatures available and the number set for Log, Block, Disabled. | |||
** Updates. The last time signatures were updated and the last time a check was performed. Updates do not neccessarily occur on each check. | |||
{{ServiceAppScreenshot|intrusion-prevention|status}} | {{ServiceAppScreenshot|intrusion-prevention|status}} | ||
Revision as of 15:00, 12 November 2018
 Intrusion Prevention Intrusion Prevention
|
|
About Intrusion Prevention
Intrusion Prevention is an Intrusion Detection system that detects malicious activity on your network. To detect malicious activity, Intrusion Prevention uses signature detection, a method that draws upon a database of known attack patterns. If Intrusion Prevention detects malicious activity, the session for that activity can be logged or blocked.
Note: Intrusion Prevention installs but is off by default.
Note: Intrusion Prevention requires at least 2 gigabytes of RAM.
Signatures & Actions
A signature matches behavior patterns such as plain text in a connection or the number of times a particular host attempts to open TCP connections to another host. When the conditions for a signature are met, the incident is either logged to the event log without distruption to the session or blocked which both logs the incident but breaks the connection causing that session to "stop".
The default signature database is automatically populated and updated on a regular basis, usually every 2-3 days. You can add custom signatures if you wish but it is not neccessary.
While it is tempting to block all signatures, there is a high potential for false positives which could cause legitmate traffic to stop working. It is therefore recommmnted that signatures are logged, the event log reviewed, and if the incident is deemed problematic, change the signature action to block.
It may be similarly temping to log all signatures. While logging won't stop traffic it will consume system processing resources (CPU and memory) and potentially fill your event log with false positives.
A signature can also be disabled. This means is it not loaded into the engine at all.
Signature actions are set by rules. In the context of signatures, actions are recommmended only.
Rules
Rules match characteristics of signatures and if matched, set signature action as follows:
- Recommended
- Enable Log
- Enable Block if Recommended is Log
- Emable Block
- Disable
Conditions:
- Signature Identifier
- Group Identifier
- Category
- Classtype
- Message
- Protocol
- Source Address
- Source Port
- Destination Address
- Destination Port
- Any part of signature
- Custom signature
- Recommended Action
- System Memory
Variables
Variables define common attributes like the home network and ports. Under most circumstances these should be left alone.
For HOME_NET and EXTERNAL_NET, the default values ensures these are automatically calculated.
Memory
Intrusion Prevention can be memory intensive. How much is used is a combination of the number of signatures enabled for Log or Block and the amount of traffic that goes through your system.
Settings
Status
The Status tab shows the following information:
- Memory Usage. The amount of system memory the IPS engine is using compared to your installed system memory.
- Metrics. The number of blocked, logged, and scanned sessions.
- Overview. Signatures and Signature Updates.
- Signatures. Total number of signatures available and the number set for Log, Block, Disabled.
- Updates. The last time signatures were updated and the last time a check was performed. Updates do not neccessarily occur on each check.
Rules
Simply uncheck Block (and Log if you wish) and the the traffic will no longer be blocked.
- Edit: Edit the rule. This is not recommended and should only be attempted by advanced users with a strong understanding of Snort rules. Invalid or poorly written rules will negatively impact network performance.
Signatures
Intrusion Prevention provides a list of signatures that you can have Untangle Log or Block when traffic matches them. The rules are grouped by classtype and can be searched using the search field at the bottom of the page.
In most cases, you do not need to change the recommended settings. You should only need to disable a signature if that rule blocks traffic from a unique software application that you must use. CREATE RULES.
The signatures are automatically updated using the latest Snort signatures.
- SID: The signature's identifier.
- Classtype: Snort classtype (grouping) of the signature.
- Category: Snort category (grouping) for the signature.
- Msg: Name of the signature.
- Reference: Links to reference information on the attack the signature will detect (if available).
- Log/Block: Enable these to log or block traffic matching the signature.
- Edit: Modify a a custom signature from the system.
- Copy: Copy a signature. Copied signatures become part of the custom set.
- Delete: Delete a custom signature from the system.
Using the Add button, you can also add your own custom signatures to the system. This should only be attempted by advanced users with a strong knowledge of Suricata signature creation. Adding invalid or poorly written rules will negatively impact network performance.
Variables
This tab provides administrators access to Suricata variables. These variables are used in rules to specify criteria for the source and destination of a packet.
Snorts most important variable is $HOME_NET. $HOME_NET defines the network or networks you are trying to protect - it is computer automatically based on your network configuration - it includes all local networks (including aliases).
Using the Add button, custom variables can be added. Adding variables may be used by users adding their own rules.This should only be attempted by advanced users with a strong knowledge of Snort signature creation.
Updates
Signatures are automatically updated every night. Any rule modifications the administrator has made will remain. New signatures are added with recommended actions.
Reports
The Reports tab provides a view of all reports and events for all traffic handled by Intrusion Prevention.
Reports
This applications reports can be accessed via the Reports tab at the top or the Reports tab within the settings. All pre-defined reports will be listed along with any custom reports that have been created.
Reports can be searched and further defined using the time selectors and the Conditions window at the bottom of the page. The data used in the report can be obtained on the Current Data window on the right.
Pre-defined report queries: {{#section:All_Reports|'Intrusion Prevention'}}
The tables queried to render these reports:
Related Topics
Snort - Writing Good Snort Rules
Intrusion Prevention FAQs
Is Intrusion Prevention based on an open source project?
Yes, Intrusion Prevention is based on Suricata.
Why is there no reference information for a specific signature?
If there is no information link available for a specific signautre, you can try searching the signature ID at Suricata Rules for more info.
Why aren't most of Intrusion Prevention's signatures blocked by default?
Because many signatures can block legitimate traffic in addition to malicious exploits we don't enable blocking by default.
You're free to change the action of any rule to block signatures as you see fit for your network.
Can Intrusion Prevention rules be configured differently within different policies?
No. Intrusion Prevention applies to all traffic flowing through NG Firewall so different configurations are not possible.
What is the difference between rule block actions?
Enable Block if Recommended is Log will only enable a signature to Block if its Recommended Action is Log.
Enable Block will unconditionally set all matching signatures to Block.
The difference is that a signature's Recommended Action (almost always either Log or Disabled) is carefully considered by the signature provider. A rule set to Enable Block if Recommended is Log will likely set that smaller and "safer" set of signatures to Block whereas Enable Block will likely set a larger set of signatures with more potential to disrupt legitimate traffic on your network.
How can I exclude network processing for signatures?
Create a variable with the network you wish to exclude in standard CIDR format such as 192.168.1.0/24. If you have multiple networks to exclude, create a comma-separated list surrounded by square brackets such as [192.168.25.1.0/24,10.10.0.0/24].
Next, create a rule to match the signatures you wish to exclude. For Action select Whitelist and then specify the variable you created to either Source or Destination networks.
NOTE: Unlike other Rule actions, the Whitelist action doesn't enable logging/blocking for rules. Signatures affected by Whitelist rules will still be processed by the first matching non-Whitelist Rule.
How do I extend the HOME_NET variable?
IPS attempts to determine the appropriate HOME_NET based on your network configuration but if a network doesn't appear to be in the list (mouse over the variable), you can either replace the HOME_NET variable value entirely or append to the existing using by leaving the default value and adding a comma separated list of additional CIDR formatted networks such as default,10.10.10.10/32,192.168.2.0/24.
