WireGuard VPN
 WireGuard VPN WireGuard VPN
|
|
About WireGuard VPN
The WireGuard VPN service provides virtual private networking via WireGuard, which is an open source lightweight VPN application and protocol designed to be fast, secure, and easy to configure.
Settings
This section reviews the different settings and configuration options available for WireGuard VPN.
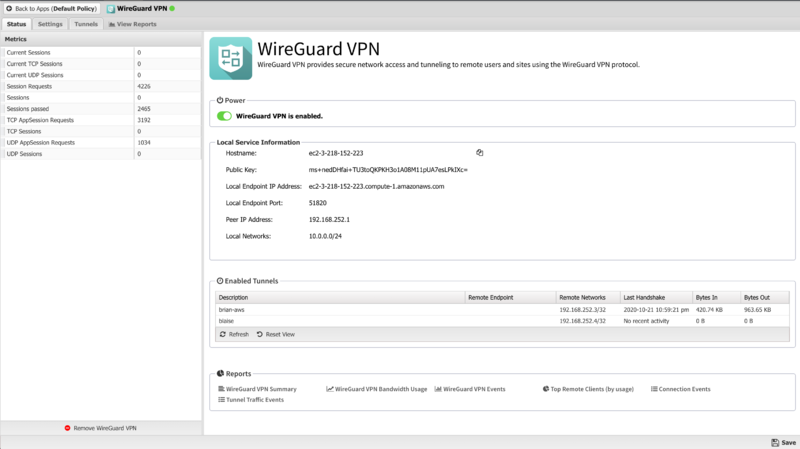
Status
The Status tab shows the status of the WireGuard VPN service
- Local Service Information
- This section displays information about the local WireGuard service such as the public key, endpoint address and port, peer address, and the list of local networks.
- Enabled Tunnels
- This section shows a list of active WireGuard tunnels.
Settings
- Listen port
- Sets the port where the WireGuard server will listen for inbound tunnel connections from peers.
- Keepalive interval
- Sets the passive keepalive interval which ensures that sessions stay active and allows both peers to passively determine if a connection has failed or been disconnected.
- MTU
- Sets the MTU size for WireGuard tunnels.
Remote Client Configuration
These fields are used when generating the Remote Client configuration.
- DNS Server
- IP Address of local DNS server that will be added to client configuration. It is initially populated using the first defined DHCP DNS Server Override address is used it found. If not, the IP address of your first non-WAN interface is used.
- Networks
- These are networks added to the client's allowed IP list. It is initially populated with all known local networks discovered from non-WAN interfaces (and their aliases) and static routes.
Peer IP Address Pool
- Assignment
- Used to select the method for address pool assignment. Can be set for Automatic to allow the system to automatically select an unused network space or Self-assigned to configure a user entered network space.
- Network Space
- Shows the automatically assigned networks space or allows editing the self-assigned network space.
- New Network Space
- Click when using Automatic assignment to select a new random network space.

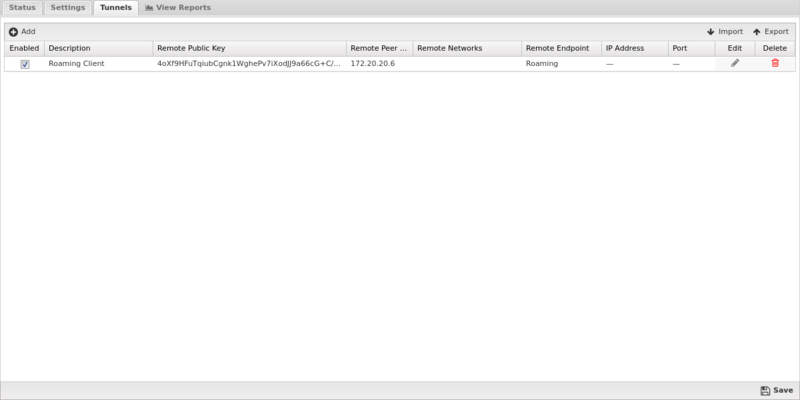
Tunnels
The Tunnels tab is where you create and manage WireGuard VPN tunnels. Each tunnel in the table has options to view the client configuration or edit the tunnel.
For a step by step guide to setting up WireGuard VPN tunnels, see Setting up WireGuard VPN site-to-site connections in NG Firewall.
- Remote Client
Clicking this icon will display a window showing the recommended client configuration in both Quick Reference (QR) Code, which many WireGuard mobile apps can scan with the devices camera and import and text file suitable for copying and pasting into the remote client.
- Tunnel Editor
- When you add a tunnel, or edit and existing tunnel, the tunnel editor screen will appear with the following configurable settings:
Note: You can copy the configuration from a remote NG Firewall peer and paste it into any of the configurable fields. The screen automatically populates all of the relevant fields from the remote side. This simplifies the configuration of tunnels and is recommended to avoid misconfiguration.
| Name | Description |
|---|---|
| Enabled | This checkbox allows you to set a tunnel to either enabled or disabled. |
| Description | This field should contain a short name or description. |
| Remote Public Key | This field is for the public key of the tunnel peer. |
| Remote Endpoint Type | This field controls the endpoint type for the peer.
|
| Remote Endpoint IP Address | Sets the IP address for a static endpoint. |
| Remote Endpoint Port | Sets the port for a static endpoint. |
| Remote Peer IP Address | This field sets the IP address that will be used by the remote peer. |
| Remote Networks | This field is used to configure the list of remote networks that should be routed across this WireGuard tunnel. Networks should be entered on per line in CIDR (192.168.123.0/24) format. |
| Monitor Ping IP Address | The IP address of a host on the remote network to ping for verifying that the tunnel is connected. Leave blank to disable. |
| Monitor Ping Interval | The time in seconds between attempts to ping the configured ping monitor address. |
| Monitor Alert on Tunnel Up/Down | When enabled, CONNECT and DISCONNECT alerts will be generated when the configured ping monitor transitions from reachable to unreachable, and unreachable to reachable. |
| Monitor Alert on Ping Unreachable | When enabled, UNREACHABLE alerts will be generated for each monitor ping that fails when the target is unreachable. |
| Local Service Information | This section includes information from the Status tab that is useful when doing copy/paste configuration between to peers. |
WireGuard VPN client
The WireGuard VPN client app is available for download on a variety of mobile device and desktop operating systems including iOS, macOS, Android, Windows, and Linux.
The download links for each supported OS are available from the WireGuard Website.
For a step by step setup guide refer to the KB article Setting up WireGuard VPN on mobile devices and desktops
Reports
The Reports tab provides a view of all reports and events for all connections handled by WireGuard VPN.
Reports
This applications reports can be accessed via the Reports tab at the top or the Reports tab within the settings. All pre-defined reports will be listed along with any custom reports that have been created.
Reports can be searched and further defined using the time selectors and the Conditions window at the bottom of the page. The data used in the report can be obtained on the Current Data window on the right.
Pre-defined report queries: {{#section:All_Reports|'WireGuard VPN'}}
The tables queried to render these reports:
Related Topics
WireGuard VPN FAQs
How resilient is a WireGuard connection?
WireGuard is built for roaming. If your device changes networks, e.g. from WiFi to a mobile/cellular, the connection will persist because as long as the client sends correctly authenticated data to the WireGuard VPN server, the server keeps the connection alive.
What cryptography is used in WireGuard?
WireGuard uses several ciphers including ChaCha20, Curve25519, BLAKE2s, SipHash24, and HKDF. For more details refer to the WireGuard Protocol & Cryptography documentation.
What transport protocol and port does WireGuard use?
WireGuard encapsulates and encrypts all data using UDP with default port 51820. There is a built-in access rule to allow WireGuard traffic on this port.