OpenVPN
 OpenVPN OpenVPN
|
|
About OpenVPN
OpenVPN enables you to create an SSL-based VPN (virtual private network) that supports both site-to-site and client-to-site tunnels. This allows your road warrior users to connect to local resources as if they were in the office, or connect the networks of several geographically distant offices together - all with the added security of encryption protecting your data. OpenVPN supports any operating system with an OpenVPN-compatible VPN client (which is almost every OS), even smartphones!
The OpenVPN application can run as a server allowing for remote clients to connect to the NG Firewall server, and the OpenVPN application can connect to other remote NG Firewall servers as a client.
The VPN Overview article provides some general guidance of which VPN technology may be the best fit for different scenarios.
Settings
This section reviews the different settings and configuration options available for OpenVPN.
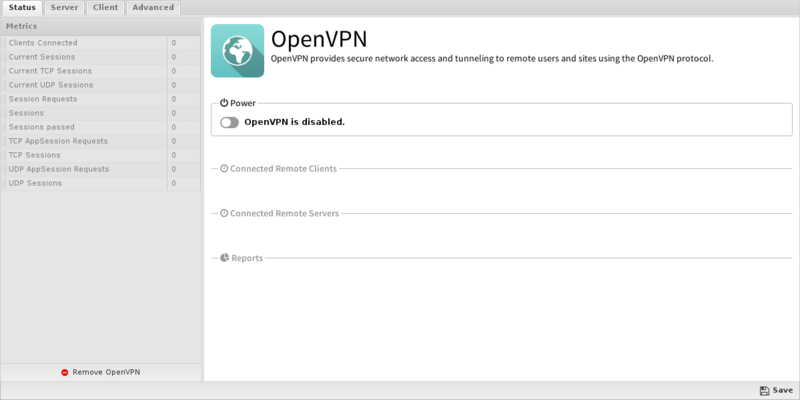
Status
The Status tab shows you a list of open connections, the time the tunnels were created and transmit statistics.
Connected Remote Clients
This grid shows the currently connected remote clients that are connected to this OpenVPN (if server is enabled.)
| Name | Description |
|---|---|
| Address | The IP of the remote client. |
| Client | The OpenVPN client name. |
| Start Time | The time that the client connected. |
| Rx Data | The amount of data received from this client in this session. |
| Tx Data | The amount of data sent to this client in this session. |
Remote Server Status
This grid shows the remote servers this OpenVPN is connecting to as a client.
| Name | Description |
|---|---|
| Name | The name of the remote server. |
| Connected | The current connection status |
| Rx Data | The amount of data received from this client in this session. |
| Tx Data | The amount of data sent to this client in this session. |
Server
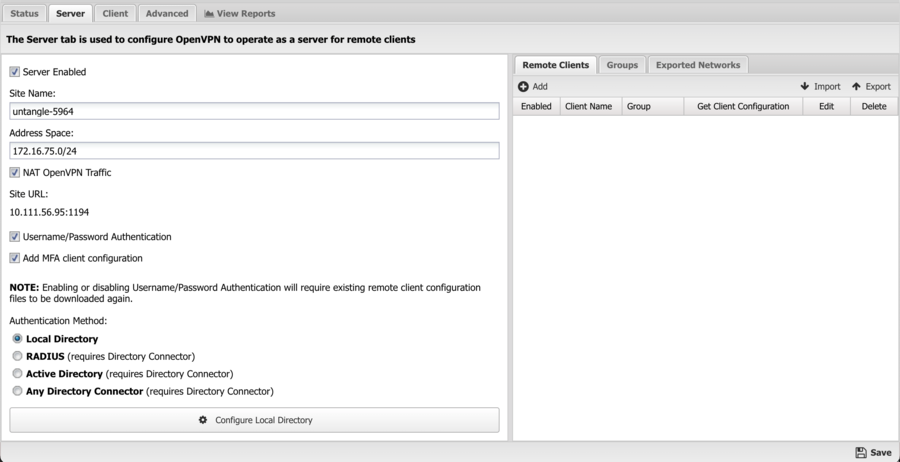
The Server tab includes all the configuration for OpenVPN's server functionality.
Site Name is the name of the this OpenVPN site. A random name is chosen so that it is unique. A new name can be given, but it should be unique across all NG Firewall sites in the organization. For example, if the company name is "MyCompany" then "mycompany" is a bad site name if you have multiple NG Firewalls deployed as it might be used elsewhere. The Site Name must be unique.
Site URL shows the URL that remote clients will use to connect to this server. This is just for reference. Verify that this address will resolve and be publicly reachable from remote networks. This URL can be configured in Config > Network > Hostname.
If Server Enabled is checked, the OpenVPN server will run and accept connections from configured Remote Clients. If unchecked the OpenVPN server will not run and not server services will be provided.
Address Space defines an IP network/space for the VPN to use internally. The Address Space must be unique and separate from all existing networks and other address spaces on other OpenVPNs. A default will be chosen that does not conflict with the existing configuration.
NAT OpenVPN Traffic will NAT all traffic from remote networks to local networks to a local address. This helps solve routing and host-based firewall issues. The default and recommended value is enabled.
Username/Password Authentication can be enabled to activate two factor authentication, requiring clients to also provide a username and password when connecting.
Add MFA client configuration can be enabled to activate multi-factor authentication using a TOTP app. This feature uses the Local Directory users and requires each user to be configured with multi-factor authentication and paired with a TOTP app.
Authentication Method is used to select the authentication method for clients when Username/Password authentication is enabled.
Remote Clients
The Remote Clients sub-tab configures all the Remote Clients that can connect to this OpenVPN server. A Remote Client is any entity that connects to this OpenVPN server as a client. This includes both remote desktops, laptops, devices, road warriors, etc. This also includes remote OpenVPNs and remote NG Firewall networks.
Initially there are no clients that are allowed to connect and an unique entry must be created for each remote client you wish to allow to connect to this server.
To add a new Remote Client click on the Add and provide the following information:
- Enabled - If checked, this client is enabled. If unchecked, this client is disabled and can not connect.
- Client Name - A unique name for the client. (alphanumerics only)
- Group - The group for this client. More information below.
- Type - The type of this client. Individual Client for a single host like a remote desktop or laptop. Network for an entire remote network that the server should also be able to reach.
- Remote Networks - The remote network in CIDR notation if this remote client is of type Network. For example: 192.168.1.0/24 means that the 192.168.1.* network lives behind the remote client and should be reachable from the server. If there are multiple networks reachable through this remote client, a comma separated list of CIDR networks can be used. These networks are automatically exported such that hosts on the main network and other remote clients can reach these networks.
After configuring this information save the new Remote Client by clicking OK then Apply. After saving settings, click on the Download Client button in the Remote Clients table on the row for the new client. This will provide links to download the configuration profile for the configured client.
- Click here to download this client's configuration zip file for other OSs (Apple/Linux/etc). provides a zip file with the OpenVPN client configuration files. This file can be used to configure various OpenVPN clients for various OSs, like linux, apple, and even some phones/tables/devices.
- Click here to download this client's configuration file for remote OpenVPN clients. provides a zip file with the OpenVPN client configuration for setting up a remote OpenVPN application to connect as a client to this server. For more information about how to install this on the remote client read the OpenVPN#Client documentation below.
- Click here to download this client's configuration onc file for Chromebook. provides a onc file that can be used to configure your Chromebook as a client to connect to the NG Firewall OpenVPN server. On the target device, browse to chrome://net-internals and use Import ONC file.
On the client system, you must first install the OpenVPN client. You can download client from here: https://openvpn.net/download-open-vpn/. After installing the OpenVPN client on the remote client, you can import the OpenVPN profile into the client.
Note: A client can only be connected once. If you install the same client on multiple remote devices they will kick each other off when a new one logs in. In most cases you need to setup a client for each remote device.
Groups
Groups are convenience feature to "group" clients together and apply some settings to that entire group. By default there will be a Default Group. Each group has the following settings:
- Full Tunnel - If checked, remote clients will send ALL traffic bound to the internet through the VPN. This allows for NG Firewall to filter ALL internet traffic for connected clients by "proxying" it through the VPN and then out through NG Firewall's internet connection. This will have no effect on remote OpenVPN clients. If unchecked, then only traffic destined to the local network are subject to filtering.
- Push DNS - If enable, OpenVPN will "push" some DNS configuration to the remote clients when they connect. This is useful if you wish for some local names and services to properly resolve via DNS that would not publicly resolve.
- Push DNS Server - If set to OpenVPN Server then the IP of the NG Firewall server itself will be pushed to the remote clients and all remote clients will use NG Firewall for all DNS lookups. If Custom is selected then one or two DNS entries can be specified that will be used for DNS resolution.
- Push DNS Custom 1 - If Push DNS Server is set to custom, this IP will be pushed to remote clients to use for DNS resolution. It is important to export this address if that traffic should travel through the VPN tunnel. If this value is blank nothing will be pushed.
- Push DNS Custom 2 - Just like Push DNS Custom 1 except this sets the secondary DNS value. If blank, no secondary DNS will be pushed.
- Push DNS Domain - If set this domain will be pushed to remote clients to extend their domain search path during DNS resolution.
These settings will apply to all clients belonging to that group. Many sites will only have one group because all clients need the same settings. However, some clients have some Full Tunnel remote clients and some Split Tunnel remote clients. In this case, you need two groups where each client belongs to the appropriate group.
Exported Networks
Exported Networks is a list of networks that are reachable through the OpenVPN server for remote clients. Exported Networks are routes that are pushed to remote clients when they connect effectively telling remote clients to reach the specified network through the OpenVPN server.
For example, exporting 1.2.3.4/24 will result in all 1.2.3.* traffic going through the OpenVPN server.
The Exported Networks grid is pre-populated on installation with the IP/netmask of each static non-WAN interface.
- If Enabled is checked this network will be exported/pushed to connecting remote clients.
- Export Name is a name, purely used for documentation purposes.
- Network is the network, in CIDR notation.

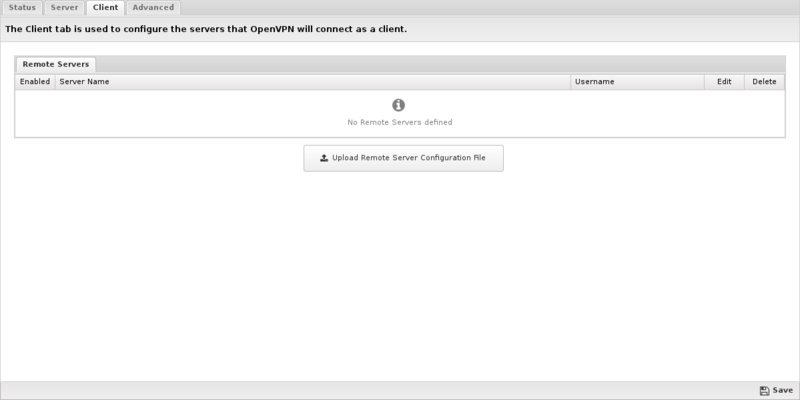
Client
The Client tab is used to configure which remote servers this OpenVPN will connect to as a client.
Remote Servers
The Remote Servers grid lists the currently configured remote servers that OpenVPN is configured to connect to.
To configure a new server to connect to, first login to the remote server and configure a new client as described above and click on the Download Client as described above in the OpenVPN#Remote_Clients section. After you have downloaded the distribution zip file return to this OpenVPN and click on the Browse button below the Remote Servers grid. Select the zip file downloaded from the OpenVPN server and then press OK. Next press the Submit button to upload the zip file to OpenVPN which will add a new entry into the Remote Servers grid based on the configuration in the submitted zip file.
If the remote server requires Username/Password authentication, you will have to edit the configuration, enabled the Username/Password authentication checkbox, and enter the username and password to be used when establishing the connection.
Once connected to a remote server, you will be able to reach their exported networks. They will also be able to reach the networks on this server specified as the Remote Network in the OpenVPN#Remote_Clients configuration.
- Note: Site to Site connections are not full-tunnel even if selected in the Group for the site to site. Internet traffic on the remote site will exit through its local gateway.
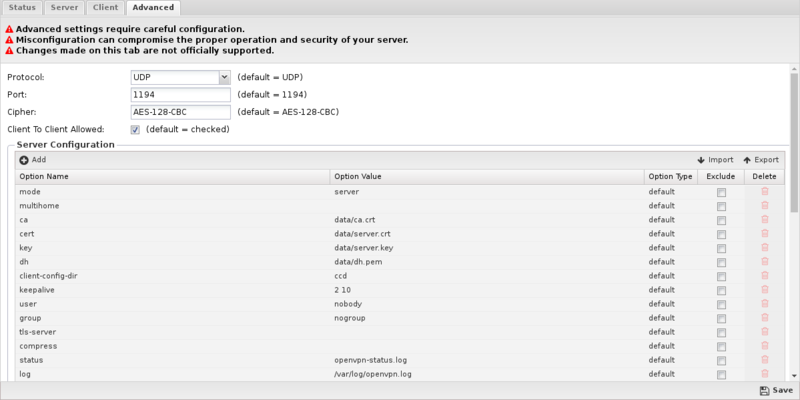
Advanced
The Advanced tab is provided for advanced users who have a detailed knowledge and understanding of OpenVPN, and need very specific configuration changes to address unique or unusual situations. It is entirely possible to completely break your OpenVPN configuration with a single wrong character, misplaced space, or by changing a configuration option that probably shouldn't be changed. Changes you make on this page can possibly compromise the security and proper operation of your sever, and are not officially supported.
Common Settings
At the top of the Advanced page are the Protocol, Port, and Cipher options. These must be the same on both the client and server for connections to work. Since they are the options most frequently modified, they can be easily configured here and will apply to both the client and server.
The Client to Client Allowed checkbox is used to enable or disable traffic passing between OpenVPN clients. When enable, all clients will have full network access to each other when connected. If disabled, traffic will not be allowed to flow between connected clients.
Server Configuration and Client Configuration
If you require changes to other low level parameters, the Server Configuration and Client Configuration grids allow you to effectively have total control of the OpenVPN configuration file that is generated. Both grids work the same way, with each configuration applied to the corresponding server or client openvpn.conf file respectively.
Both lists contain config items comprised of a Option Name and Option Value pair. By default, all items in both configuration grids are read only. The lists represent the default configuration settings used for the server and client configuration files. The default items cannot be modified or deleted, they can only be excluded. When you exclude an item, it is effectively removed from the resulting configuration file. To change one of the default items, simply add a new item with the same Option Name, and input the Option Value that you want to be used. This will effectively override the default. The same method can also be used to add configuration items that are not included in the default list.
Exclude Default Configuration Item
- This example shows how to disable the comp-lzo option in the server configuration file to turn off compression:
Modify Default Configuration Item
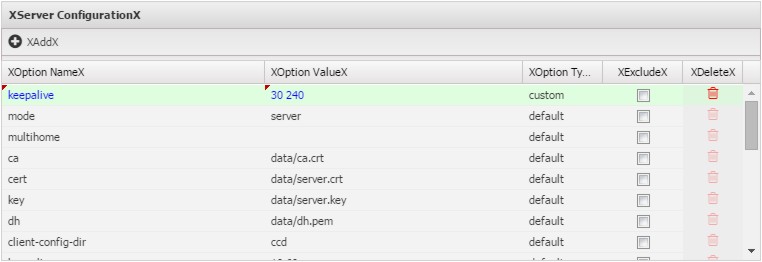
- This example shows how to change the default keepalive setting in the server configuration file:
Add New Configuration Item
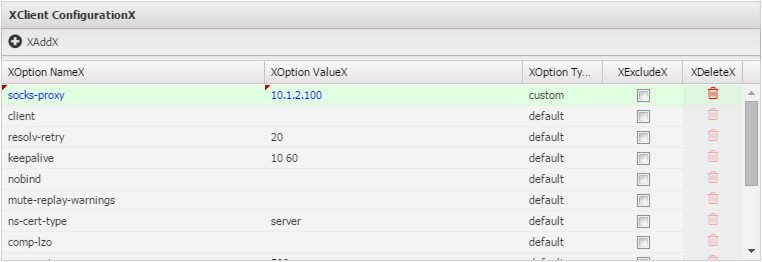
- This example shows how to add a socks-proxy setting to the client configuration file:
Reports
The Reports tab provides a view of all reports and events for all connections handled by OpenVPN.
Reports
This applications reports can be accessed via the Reports tab at the top or the Reports tab within the settings. All pre-defined reports will be listed along with any custom reports that have been created.
Reports can be searched and further defined using the time selectors and the Conditions window at the bottom of the page. The data used in the report can be obtained on the Current Data window on the right.
Pre-defined report queries: {{#section:All_Reports|'OpenVPN'}}
The tables queried to render these reports:
- [[Database_Schema#openvpn_stats|openvpn_stats]
- openvpn_events
Related Topics
OpenVPN FAQs
Download Links
OpenVPN supports most operating systems. Download the appropriate client from the links below.
Deployment instructions are here: Configure and deploy OpenVPN Clients for remote users
Microsoft Windows
You can download the Windows client from here: https://openvpn.net/community-downloads/.
Apple macOS
You can download the macOS client here: https://openvpn.net/client-connect-vpn-for-mac-os/
Linux
A Linux client is available here: https://openvpn.net/openvpn-client-for-linux/
Chrome OS
Steps to install OpenVPN on Chrome OS devices:
https://support.untangle.com/hc/en-us/articles/207304818-Deploy-the-OpenVPN-Client-to-a-Chromebook
iOS Mobile Devices

For iPhones, we suggest OpenVPN Connect available on iTunes https://itunes.apple.com/us/app/openvpn-connect/id590379981?mt=8
- Install OpenVPN Connect app on your iPhone or iPad.
- Login to the NG Firewall server, download the client config file by selecting "client configuration zip for other OSs".
- Unzip the config file.
- Open iTunes and select the .ovpn, .crt, and .key files from the config zip to add to the app on your iPhone or iPad.

Android Mobile Devices
You can download the OpenVPN Connect client app from the Google Play Store: https://play.google.com/store/apps/details?id=net.openvpn.openvpn
Other FAQs
Is there a way to set up a password for the OpenVPN users?
Yes, if you right-click on the OpenVPN icon on the client's PC there is an option for a password. Please note this password is only used when launching the client.
How can I restrict access to certain OpenVPN users?
By default, OpenVPN users can connect to any machine that the NG Firewall can connect to. However, routes are pushed to all the "Exported" network automatically. Be aware that nothing prevents remote users who have administrator access to their machines from adding routes manually.
If restricting access to OpenVPN users is a concern, Firewall rules or Filter Rules can be used. In the Firewall app, the easiest way is to create a block rule blocking traffic when Source Interface == OpenVPN. Above that rule, create rules to allow traffic when Username is the OpenVPN user you want to allow to the desired locations. In this scenario OpenVPN traffic will be blocked into your network except for explicitly allowed traffic.
Using rules you can limit access to certain resources to only the desired remote users.
Can I create site-to-site tunnels with non-NG Firewall devices?
When using OpenVPN for site-to-site tunnels we only support using other NG Firewall endpoints. Some users have had success with DD-WRT and Tomato, but this is not supported by the Support team. If you need to connect a VPN tunnel to an endpoint that isn't another Arista ETM device, we recommend using IPsec VPN.
I'm using site-to-site and my software clients can only talk to the main server. Why?
If you have both software clients on the road and site-to-site tunnels, the software clients will only be able to see your main site by default. To allow them to transit the tunnel(s) to other sites, simply add the VPN Address Pool to the Exported Hosts and Networks. After this is done, software clients will be able to reach all exported sites.
How can I allow software clients to resolve DNS over the tunnel?
To allow DNS resolution for remote clients you'll need to modify some OpenVPN settings - if NG Firewall is doing DNS resolution on your network, simply check Push DNS in OpenVPN Settings > Server > Groups > Group Name for any groups you want to push DNS settings to. Configure the DNS settings you would like pushed to the remote clients. You may need to use the FQDN when accessing resources across the tunnel.
Clients are getting disconnected after 60 seconds. Why?
Did you share the same client config between multiple machines? If both are running simultaneously, they will conflict: when the second connects the first is disconnected. After 60 seconds, the first will reconnect and disconnect the second. This repeats endlessly. Do not share the same client config with multiple machines.
I'm setting up a new client and can't connect. Why?
Make sure that the IP that the client is connecting to is the public IP of the server, or that the traffic to that IP on port 1194 is being forwarded to your server. Also make sure you are testing from the outside. By default the Access Rules block OpenVPN clients from connecting to a server from one of its own LANs. This is to prevent clients from losing connectivity while on the local network because of a routing loop.